What is design risk? To “design” is to create, fashion, execute or construct according to plan. The term design as used here refers to the entire scope of a project. A business system design is a collection of design documents and supporting materials which define the system functionality that supports one or more business processes and in the process, creates, retrieves, updates and deletes data.
The 3 Components of a Successful Systems Design
Topics: IT Audit, IT Governance, IT Infrastructure, IT Strategy, IT Risk, IT Controls, Performance Management/Measurement
What is Transaction Authenticity?
What is Transaction Authenticity?
Transaction authenticity can be defined as the authentication of a party’s (individual, organization) identity, to ensure that pending transactions and contractual agreements are legal and enforceable.
Topics: IT Audit, IT Infrastructure, Cloud Computing, IT Risk, IT Controls, Performance Management/Measurement
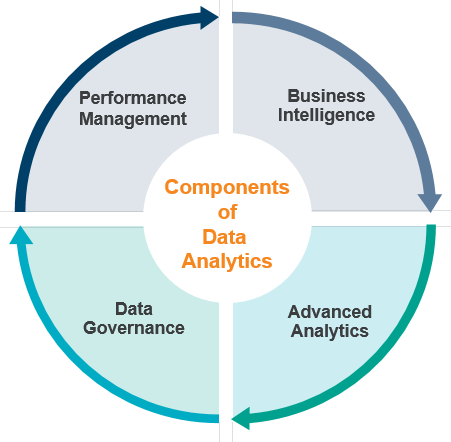
Guide to the State of Data Analytics
What is Data Analytics?
Data analytics is the practice of embedding insight into operations to drive business strategy and performance.
Topics: IT Audit, Data Analytics
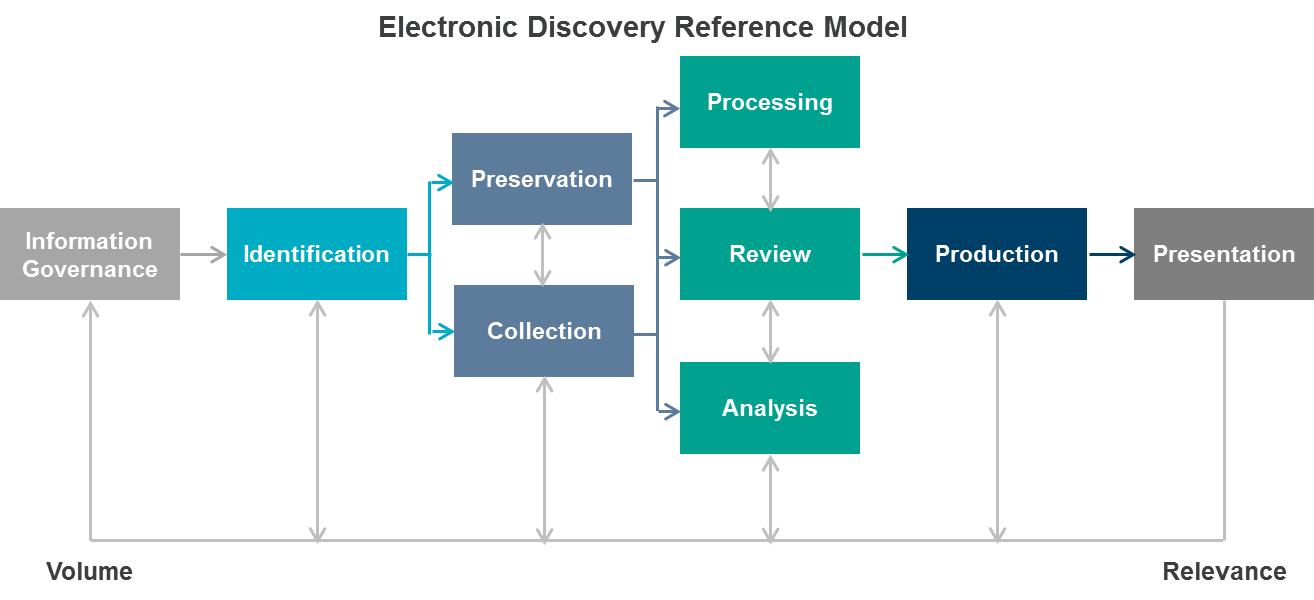
Electronic Discovery Risks, Challenges and Procedures
Electronic discovery (eDiscovery) refers to the process of searching, locating and securing electronic data for the purpose of using it as evidence in a legal case.
Topics: Laws & Regulations, IT Audit, IT Security, IT Controls, Investigations/Forensics
Add a Comment: